How it works
The MCP server implements the following standards:| Standard | Purpose |
|---|---|
| OAuth 2.1 | Authorization framework |
| Dynamic Client Registration (RFC 7591) | Each AI client registers automatically — no manual provisioning |
| PKCE | Proof Key for Code Exchange protects the authorization flow |
| JWT | Access tokens are JWTs verified against Userplane’s JWKS endpoint |
mcp:tools.
What happens when you connect
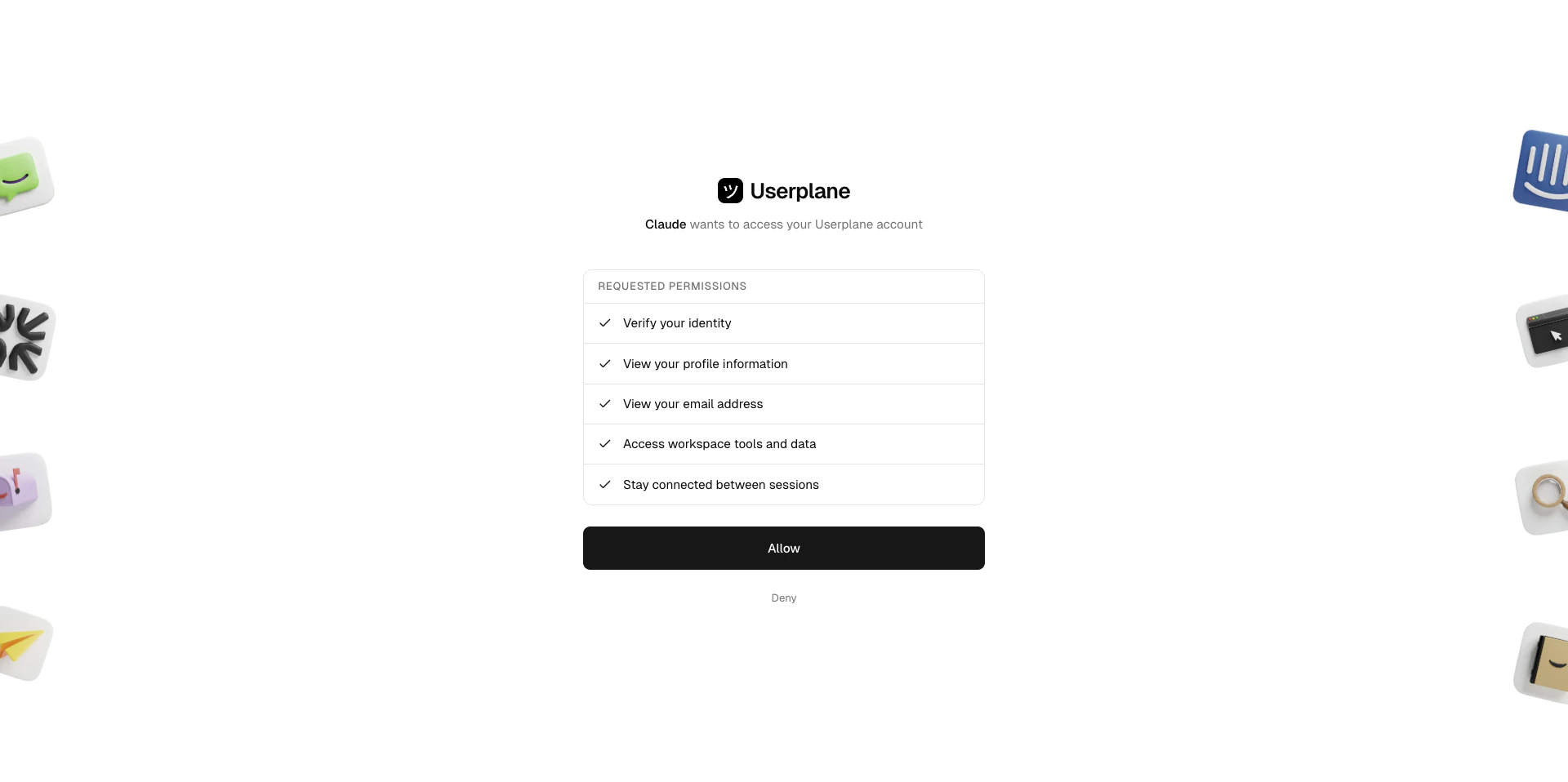
First tool call triggers OAuth
When you ask your agent to do something that requires Userplane data, the client initiates the
OAuth flow.
Permissions
MCP tools respect the same workspace roles as the Userplane dashboard and REST API.| Capability | Required role |
|---|---|
| Read data (list, get, show) | Any workspace member |
| Create recording links | Any workspace member |
| Update recording links | Any workspace member |
| Delete recordings | Admin, Owner, or creator |
| Delete recording links | Admin, Owner, or creator |
Your workspace role determines what operations are available through the MCP server. If you
receive a permission error, check your role in Workspace Settings >
Team.
Security
- Per-client registration — each AI client (Claude, Codex, Cursor, VS Code, ChatGPT) registers as a separate OAuth client. Revoking one client’s access does not affect others.
- Token scoping — access tokens are scoped to
mcp:toolsand carry no broader permissions. - JWT verification — every request is verified against Userplane’s JWKS endpoint with issuer and audience checks.
- No shared secrets — no API keys or client secrets are shared with the AI client. All clients use PKCE (public client flow).
Managing connections
Each authorized MCP client appears in your account’s Connected Apps list. From there you can review permissions, check authorization dates, and revoke access. To revoke a specific client’s access:- Go to Account Settings > Connections.
- Locate the client and open the actions menu (three dots).
- Select Revoke Access, type the application name to confirm, and click Revoke.
For the full walkthrough including screenshots, see Connected Apps.
The Userplane REST API uses
uspl_ API keys for authentication (see API
Authentication). The MCP server uses OAuth 2.1 instead — the two
authentication methods provide access to the same underlying resources through different
interfaces.Related articles
- Userplane MCP — overview of the workspace MCP server.
- Getting Started — connect your AI client and start analyzing recordings.
- Connected Apps — view and revoke MCP client access from Account Settings.
- API Authentication — REST API authentication with
uspl_API keys. - Roles & Permissions — full breakdown of workspace roles.